SSH access doesn’t work when OpenVPN client is enabled on DD-WRT.
Packages do arrive at the router if you try to SSH against the WAN IP, however, because all OUTPUT traffic is diverted through the VPN (interface tun0) SSH won’t succeed.
What’s missing is an OUTPUT rule on iptables to route traffic on port 22 through the vlan2 interface (that’s the interface connected directly to the internet).
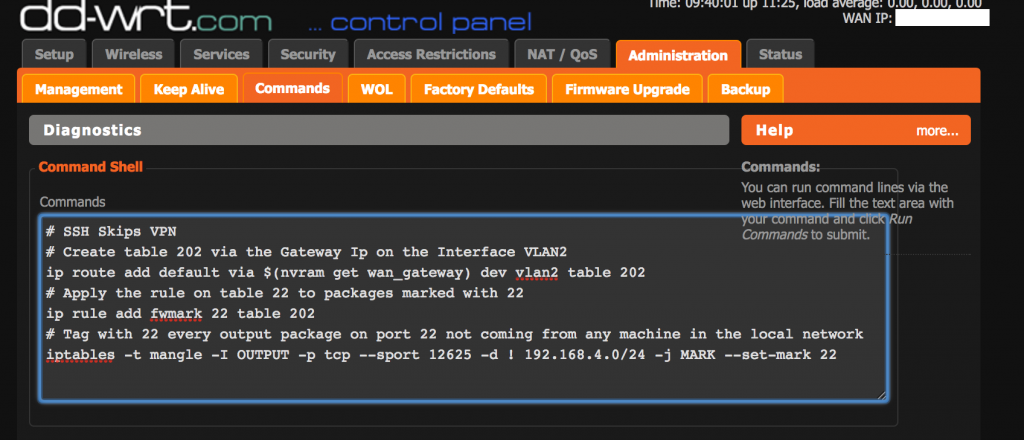
First, create table 202 via the Gateway Ip on the Interface VLAN2:
$ ip route add default via $(nvram get wan_gateway) dev vlan2 table 202
Then apply the rule on table 202 to packages marked with 22.
$ ip rule add fwmark 22 table 202
Finally, tag with 22 every output package on port 22 not coming from any machine on the local network.
$ iptables -t mangle -I OUTPUT -p tcp --sport 22 -d ! 192.168.1.0/24 -j MARK --set-mark 22
Note that the last command skips packages from the local network in my case 192.168.1.0/24, reason being that when SSHing from a host in local, the packages should be routed through br0 and not vlan2.
First issue these commands in the command line of your router to ensure they work with you, if somehow they break your routing, a restart will clear them. Once you have made sure they work, you can add them to the firewall script of your router. Note also that some DDWRT versions won’t apply the iptables rules until all services are restarted.
Note that my config IP and port is different because I am not using the default values.
For reference, this is how my Firewall section script looks like:
# Create a rule to skip the VPN echo 0 > /proc/sys/net/ipv4/conf/all/rp_filter iptables -t mangle -F PREROUTING ip route add default table 200 via $(nvram get wan_gateway) ip rule add fwmark 1 table 200 ip route flush cache ## SSH to decice (port 12601) # First the port forwarding part iptables -t nat -I PREROUTING -p tcp --dport 12601 -j DNAT --to 192.168.1.132:12601 iptables -I FORWARD -i vlan2 -d 192.168.1.132 -p tcp --dport 12601 -j ACCEPT # Now mark packages from RPI and source port 12601 with tag 1. The rule above will direct packages marked with 1 through the wan gateway iptables -t mangle -I PREROUTING -i br0 -p tcp -s 192.168.1.132 --sport 12601 -j MARK --set-mark 1